Penetration Testing,
Reimagined with AI
Trinity AI combines autonomous AI reasoning with human expert validation to deliver pentesting results in hours - not weeks. Near-zero false positives, full compliance mapping, proof-of-exploit evidence.
Rapid, Continuous Analysis
Unlike legacy pentesting, Trinity AI doesn't drown you in noise. Every finding is validated, prioritized, and shipped with proof-of-exploit evidence.
Precision Over Volume
- Correlates vulnerabilities with real exploit paths
- Removes duplicate or irrelevant scanner output
- Validates findings through multi-layer intelligence
- Flags only confirmed, high-confidence issues
- Ships proof-of-exploit evidence (screenshots, payloads, traces)
Testing Methodologies
Three Approaches. Total Coverage.
Whether you need an external audit, insider simulation, or full-depth code review - Trinity AI adapts.
Black Box Testing
Real attacker perspective with zero prior access. Simulate external threats targeting public infrastructure, APIs, and cloud-exposed assets.
- Public IP infrastructure and exposed services
- Internet-facing applications and APIs
- Cloud-exposed assets and identities
- Attack surface weaknesses and misconfigurations
Ideal for external audits, launches, and compliance validation.
Grey Box Testing
Partial knowledge to mirror trusted insiders and integration partners - balanced realism plus depth.
- Business logic flaws and privilege escalation paths
- API abuse vectors and excessive permissions
- Sensitive data exposure scenarios
Balanced realism plus depth for complex applications.
White Box Testing
Full transparency for maximum depth across code, architecture, and CI/CD pipelines.
- Secure code audits and dependency review
- CI/CD pipeline and IaC validation
- Advanced misuse-case and threat-model detection
Perfect for teams embedding security into SDLC workflows.
What We Test
Multi-Surface Coverage for Modern Cloud Teams
From infrastructure to source code, Trinity AI spans every layer attackers target - so you can ship with confidence.
IP Infrastructure Pentesting
- Open ports, exposed services, and VPN/gateway weaknesses
- Network misconfigurations and exploitable routes
- Unpatched systems plus known CVEs ready for weaponization
Web Application Pentesting
- OWASP Top 10 vulnerabilities across apps and APIs
- Authentication, authorization, and business logic flaws
- Injection attacks, broken access control, and misconfigurations
Mobile Application Pentesting
- OWASP Mobile Top 10 vulnerability assessment
- Binary analysis, API security, and data storage auditing
- Permission escalation and insecure communication detection
Source Code Security Analysis
- Insecure patterns, hardcoded secrets, and privilege escalation vectors
- Input validation gaps and cryptographic misuse
- Library and dependency risk across modern stacks
How Trinity AI Works
Five Autonomous Phases with Human Oversight
Our multi-layer engine ensures every finding is contextual, validated, and ready for remediation.
Surface Intelligence Layer
Discovers and maps your application, IP, mobile, and code assets before testing begins.
Vulnerability Reasoning Layer
Applies static, dynamic, and behavioral analysis to uncover weaknesses across all surfaces.
Validation Layer
Replicates real-world attack chains to confirm exploitability and impact with proof-of-exploit evidence.
Correlation Layer
Prioritizes issues by severity, exploitability, and business context. Maps to OWASP, NIST, ISO 27001, PCI DSS, SOC 2.
Expert Validation
Trinity AI security operators verify edge cases, complex logic, and sensitive findings - human seal of approval.
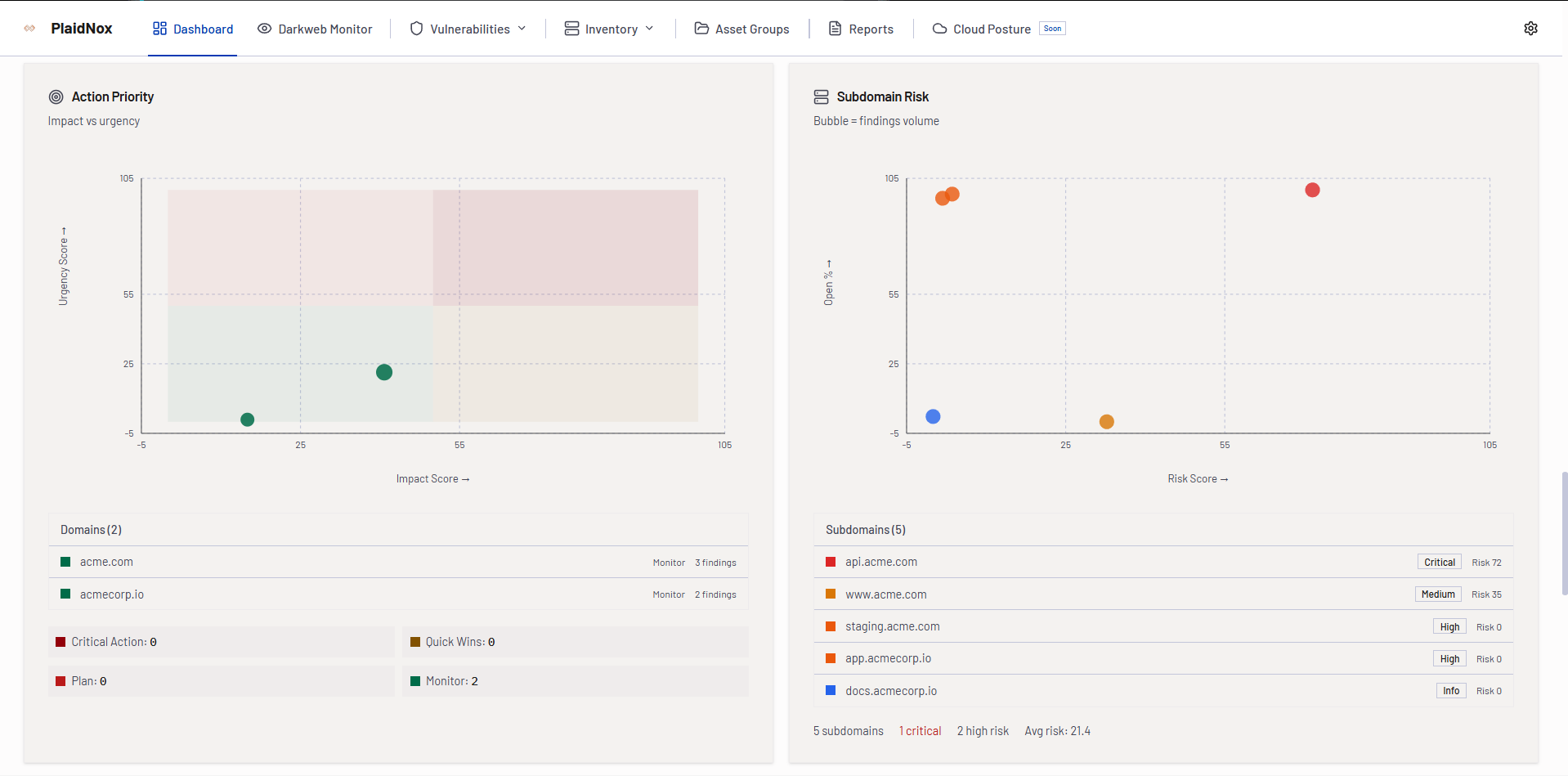
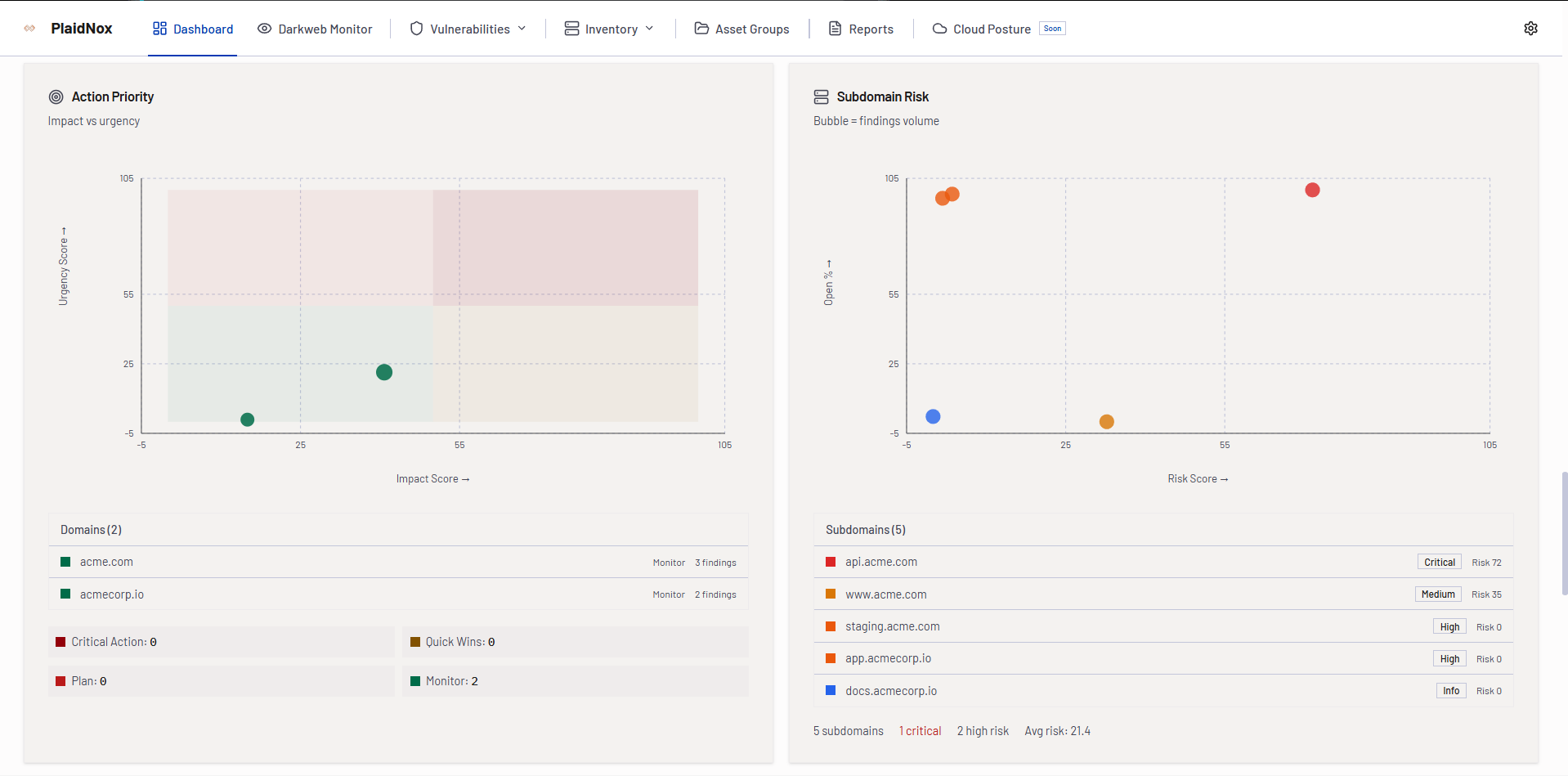
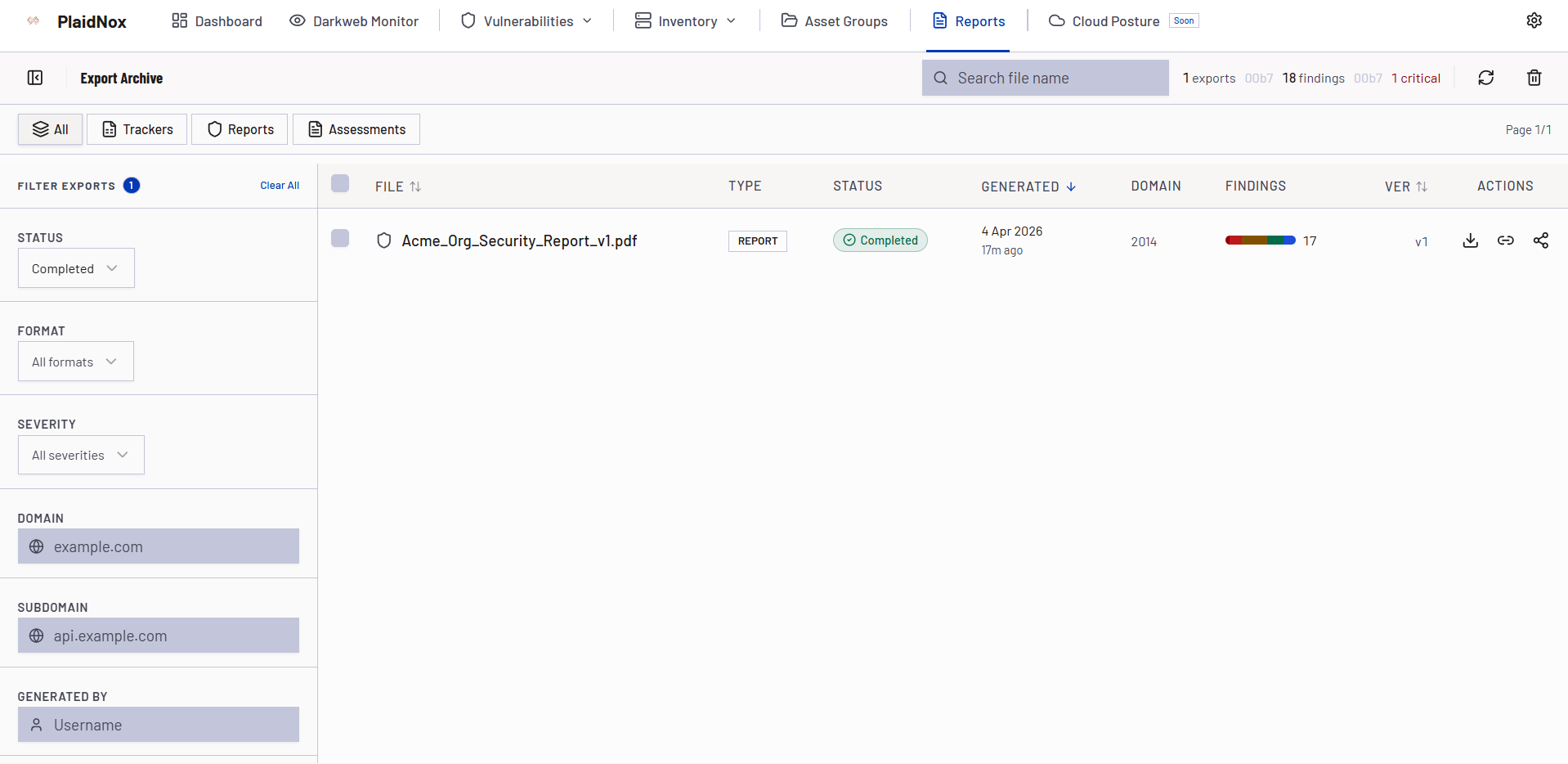
PTaaS Portal
See Trinity AI in Action
Explore the portal - from engagement overview to finding details and actionable reports.
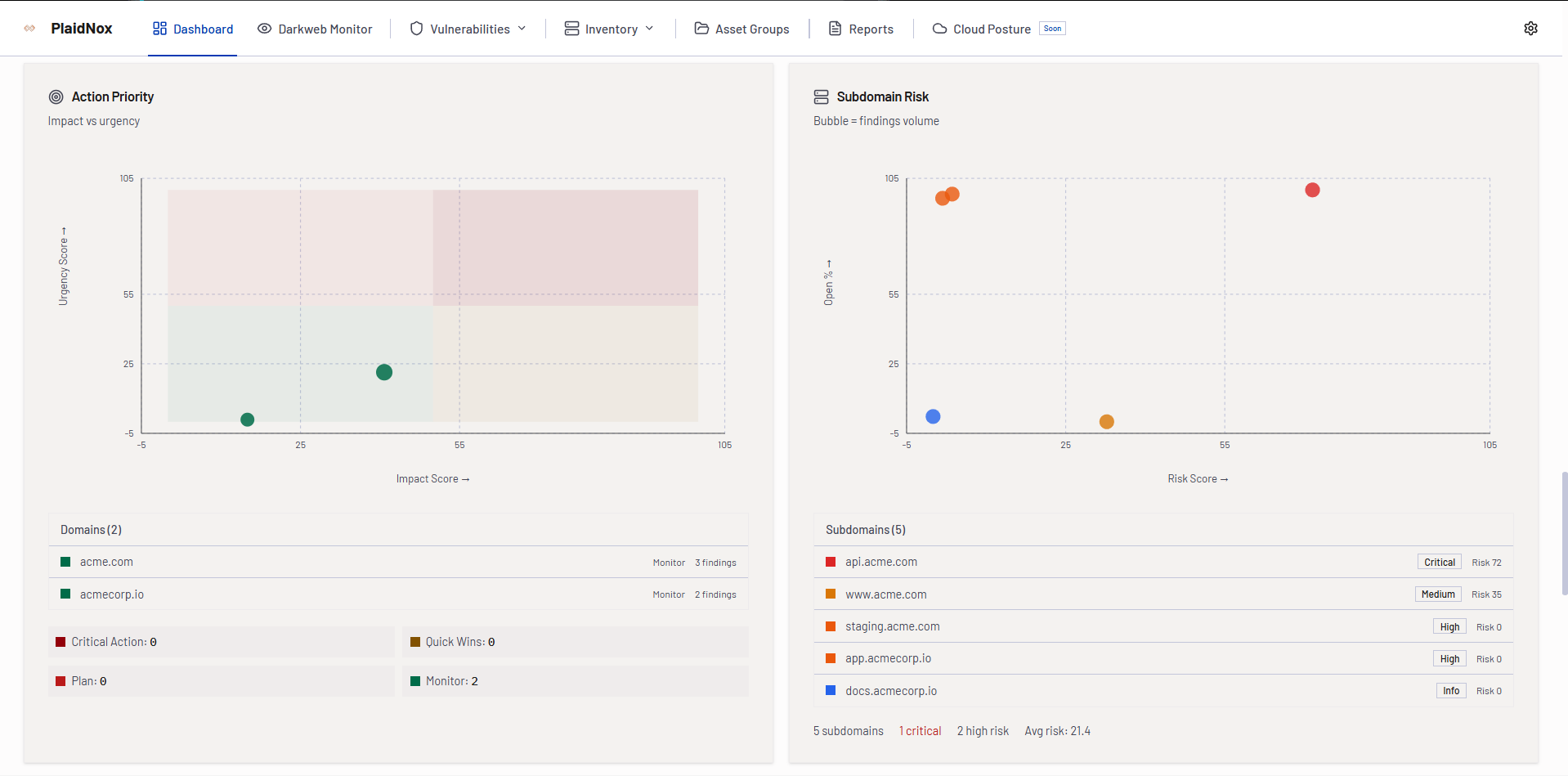
PTaaS Portal - Your Testing Command Center
Manage all penetration testing engagements, track findings in real time, communicate with testers, and download reports - all from one unified portal.
- Real-time testing progress
- Finding severity breakdown
- Engagement timeline
- Direct tester communication
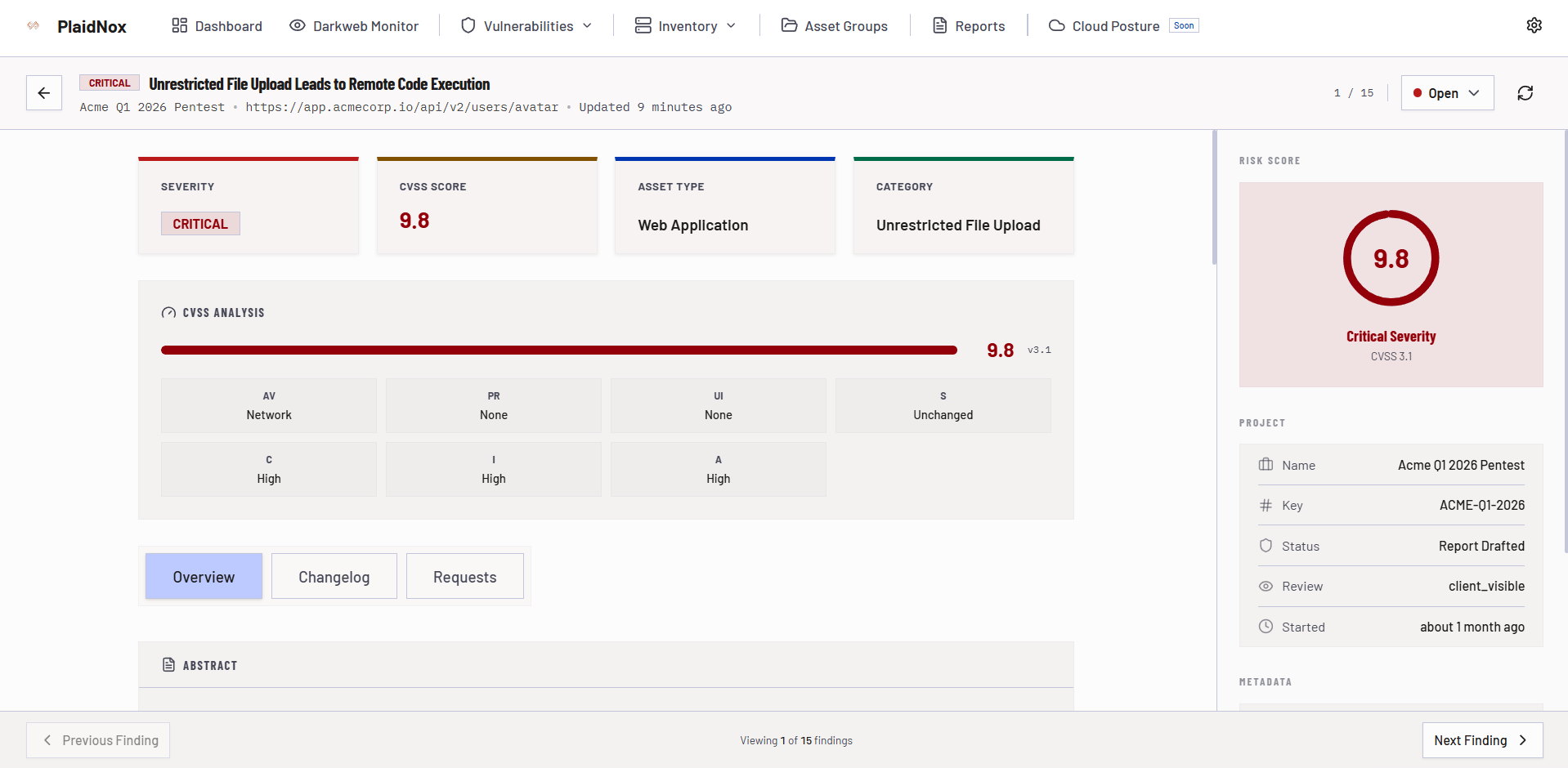
Reporting That Drives Action
Every Trinity AI assessment ships as a PDF report plus interactive web dashboard so executives and engineers share the same view of risk and remediation.
- Executive summary with business-level risk
- Technical findings plus CVSS + Trinity AI Risk Score
- Proof-of-concept evidence and reproduction paths
- Remediation guidance mapped to engineering workflows
- Compliance mapping for OWASP, NIST, ISO 27001, PCI DSS, SOC 2
Why Security Teams Choose Trinity AI
- AI-driven plus human-verified accuracy
- Near-zero false positives with actionable detail
- Coverage for IPs, web apps, mobile apps, APIs, and source code
- Supports black, grey, and white box methodologies
- Developer-friendly reports built for action
- Scales from startups to global enterprises
- Continuous testing available for ongoing validation
- Mobile application vulnerability scanning
Whether you are shipping new features, onboarding enterprise clients, or preparing for audits, Trinity AI delivers intelligent security insight that helps teams fix issues - not just find them.
Ready to See Trinity AI in Action?
Stop waiting weeks for pentesting results. Start securing faster with AI-driven assessments verified by seasoned experts.