Discover, Assess &
Secure Your Attack Surface
Veta continuously maps your assets, scans every layer - from mobile apps to cloud infrastructure - and delivers actionable intelligence so you can remediate faster.
Always-On Asset Monitoring
Unlike point-in-time scans, Veta runs continuously - discovering new assets, detecting changes, and alerting you the moment new risks emerge across your entire infrastructure.
Precision Over Volume
- Continuously discovers new assets as your infrastructure evolves
- Correlates findings across scanners for unified risk context
- Removes false positives through multi-layer validation
- Maps every finding to OWASP, NIST, ISO 27001, PCI DSS
- Ships actionable remediation steps with CVSS scoring
Veta Scanners
6 Scanner Types. Total Coverage.
From mobile apps to cloud infrastructure - Veta scans every layer of your attack surface with specialized engines.
Mobile App Scanner
Collect mobile assets and scan for OWASP Mobile Top 10 vulnerabilities. Binary analysis, API security testing, and data storage auditing.
- OWASP Mobile Top 10 coverage
- Binary & API security analysis
- Permission & data storage auditing
- Insecure communication detection
Ideal for teams shipping iOS & Android applications.
Network Scanner
Comprehensive port scanning, service detection, and CVE-on-port mapping with GeoIP visualization and ASN data.
- Port scanning & service detection
- CVE mapping per open port
- ASN / GeoIP visualization
Maps every open door in your network infrastructure.
Web Scanner
Automated web vulnerability detection - subdomain discovery, HTTP probing, intelligent crawling, and thousands of fingerprints.
- Vulnerability fingerprints
- Subdomain enumeration
- Intelligent web crawling
Thousands of fingerprints. Zero false positives.
DNS & SSL Scanner
Full DNS analysis, SSL/TLS certificate inventory, protocol & cipher strength analysis, and CSP evaluation.
- SSL certificate inventory & expiry alerts
- Protocol & cipher strength analysis
- CSP audit & DNS record validation
Certificate health. DNS records. CSP evaluation.
Dark Web Scanner
Credential leak monitoring across dark web & underground forums with blast-radius scoring and segmentation.
- Credential leak detection
- Blast radius analysis
- Employee / customer categorization
Know when your credentials surface on the dark web.
Cloud Posture Scanner
Script-based onboarding for multi-cloud security posture across AWS, Azure, and GCP with 8 compliance framework baselines.
- AWS / Azure / GCP support
- Script-based onboarding
- 8 compliance frameworks
Multi-cloud CSPM - AWS · Azure · GCP.
What We Map
Multi-Surface Coverage for Modern Cloud Teams
From web applications to cloud configurations, Veta maps every layer attackers target - so you can secure with confidence.
Web & Subdomains
- Subdomain enumeration and HTTP probing
- Web technology fingerprinting and detection
- Content security policy and header analysis
Network Infrastructure
- Open ports, services, and CVE-on-port mapping
- ASN and GeoIP geolocation intelligence
- Network misconfigurations and exploitable routes
Mobile Applications
- OWASP Mobile Top 10 vulnerability assessment
- Binary analysis, API security, and data storage auditing
- Permission escalation and insecure communication
Cloud & Certificates
- AWS, Azure, GCP misconfigurations and IAM issues
- SSL/TLS certificate health and cipher analysis
- DNS record validation and CSP evaluation
How Veta Works
Five Phases of Continuous Protection
From discovery to monitoring, Veta's multi-layer engine ensures every asset is mapped, scanned, enriched, and tracked.
Asset Discovery
Discovers and maps every asset - domains, IPs, apps, cloud resources - across your entire infrastructure.
Multi-Scanner Analysis
Runs six specialized scanners in parallel: mobile, network, web, DNS & SSL, dark web, and cloud posture.
AI Enrichment
AI-generated descriptions, remediation guidance, CVSS scoring, and compliance mapping for every finding.
Correlation & Prioritization
Correlates findings across scanners, deduplicates, and prioritizes by severity, exploitability, and business context.
Continuous Monitoring
Scheduled scans, 7 notification channels, and real-time alerts keep your security posture up to date.
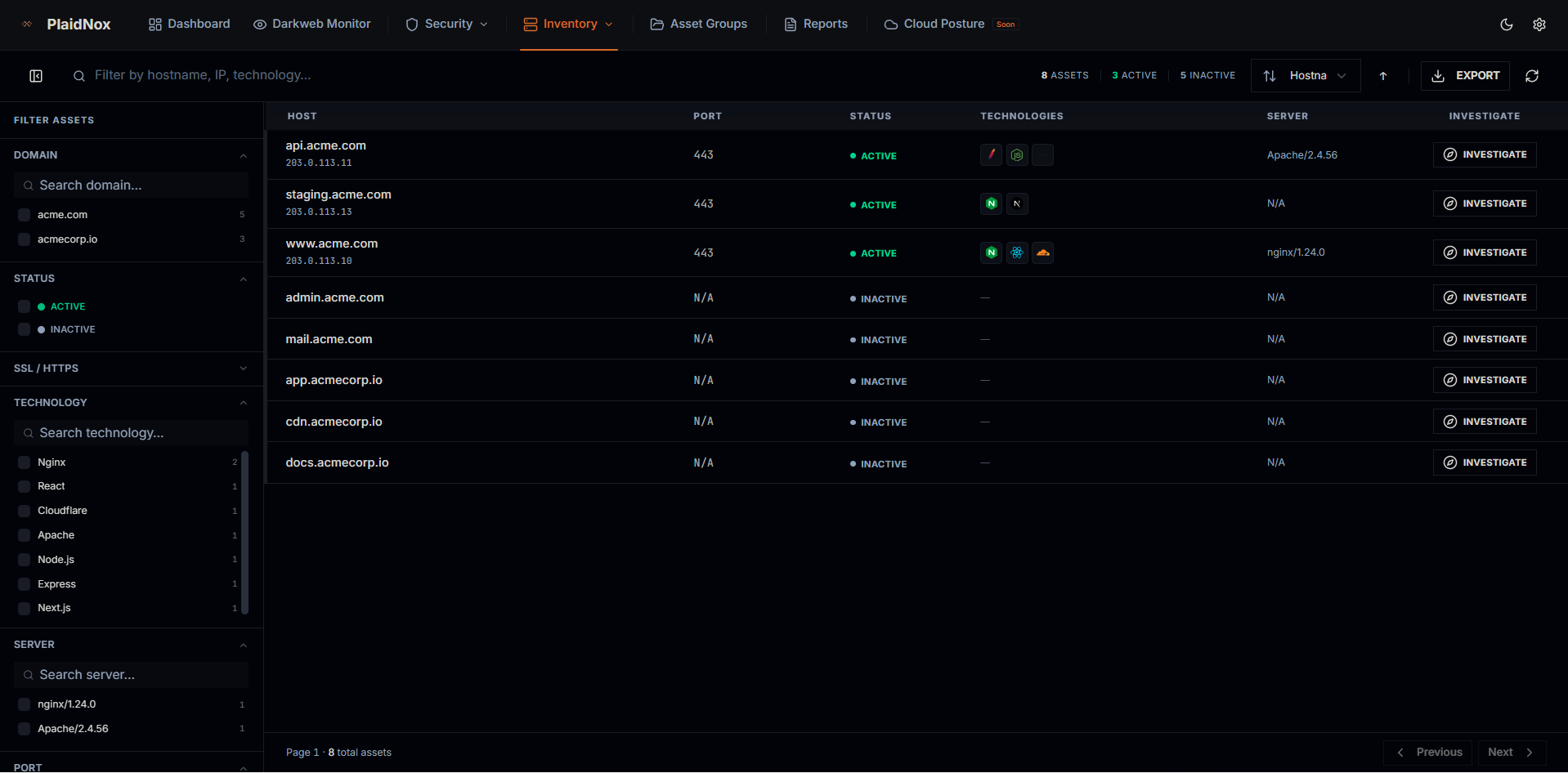
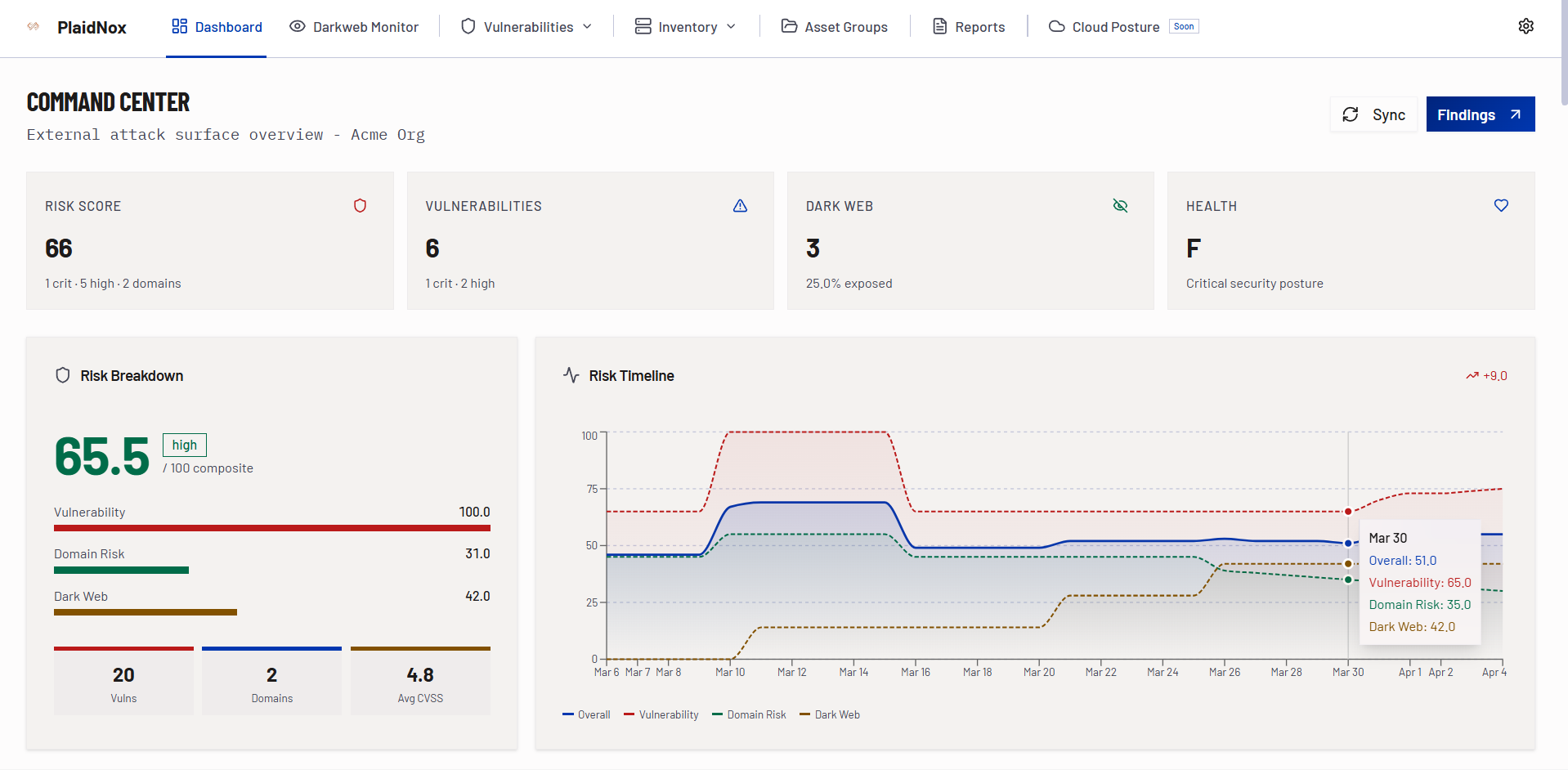
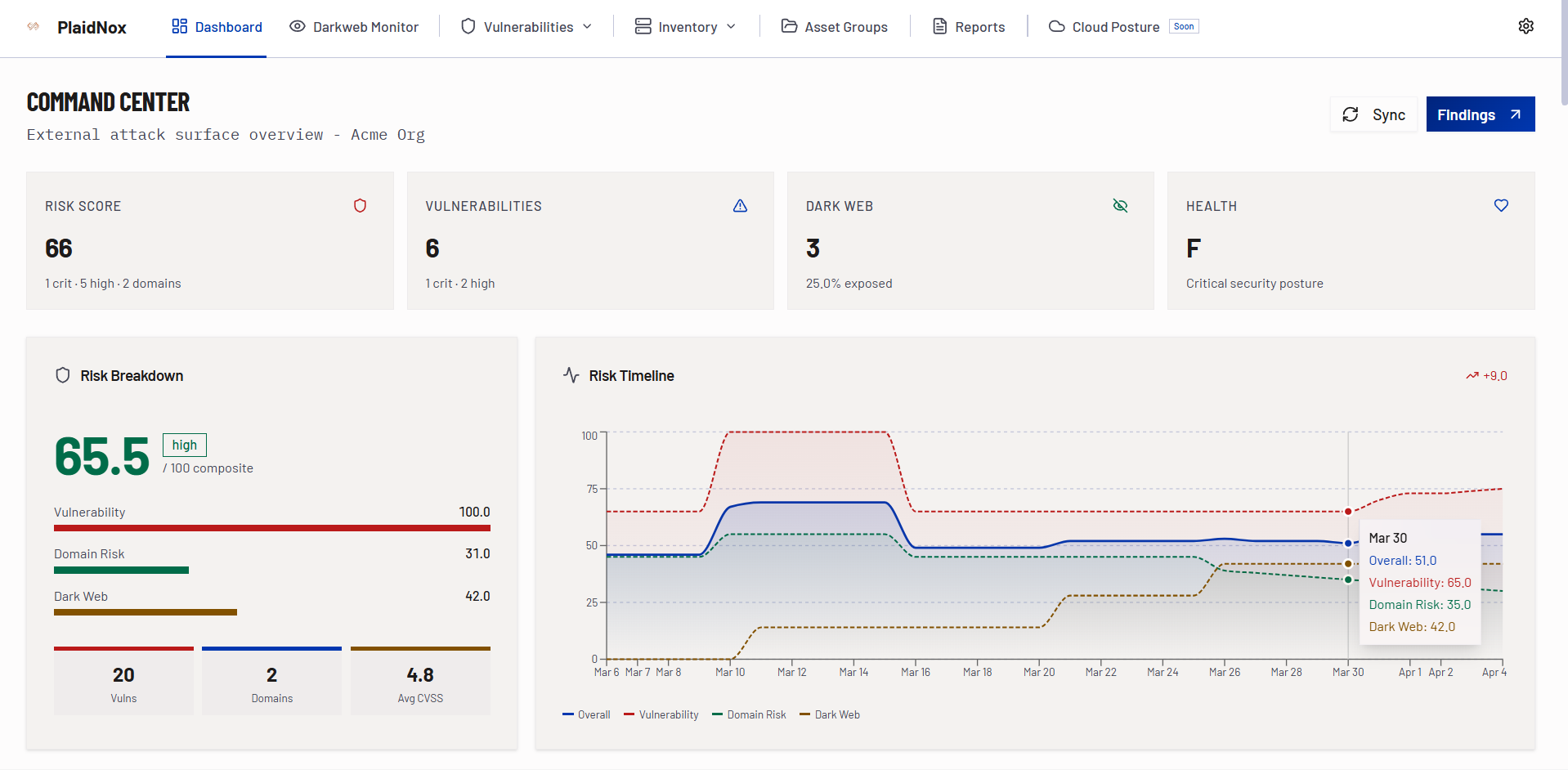
Veta Portal
See Veta in Action
Explore the platform - from the security dashboard to vulnerability details and actionable reports.
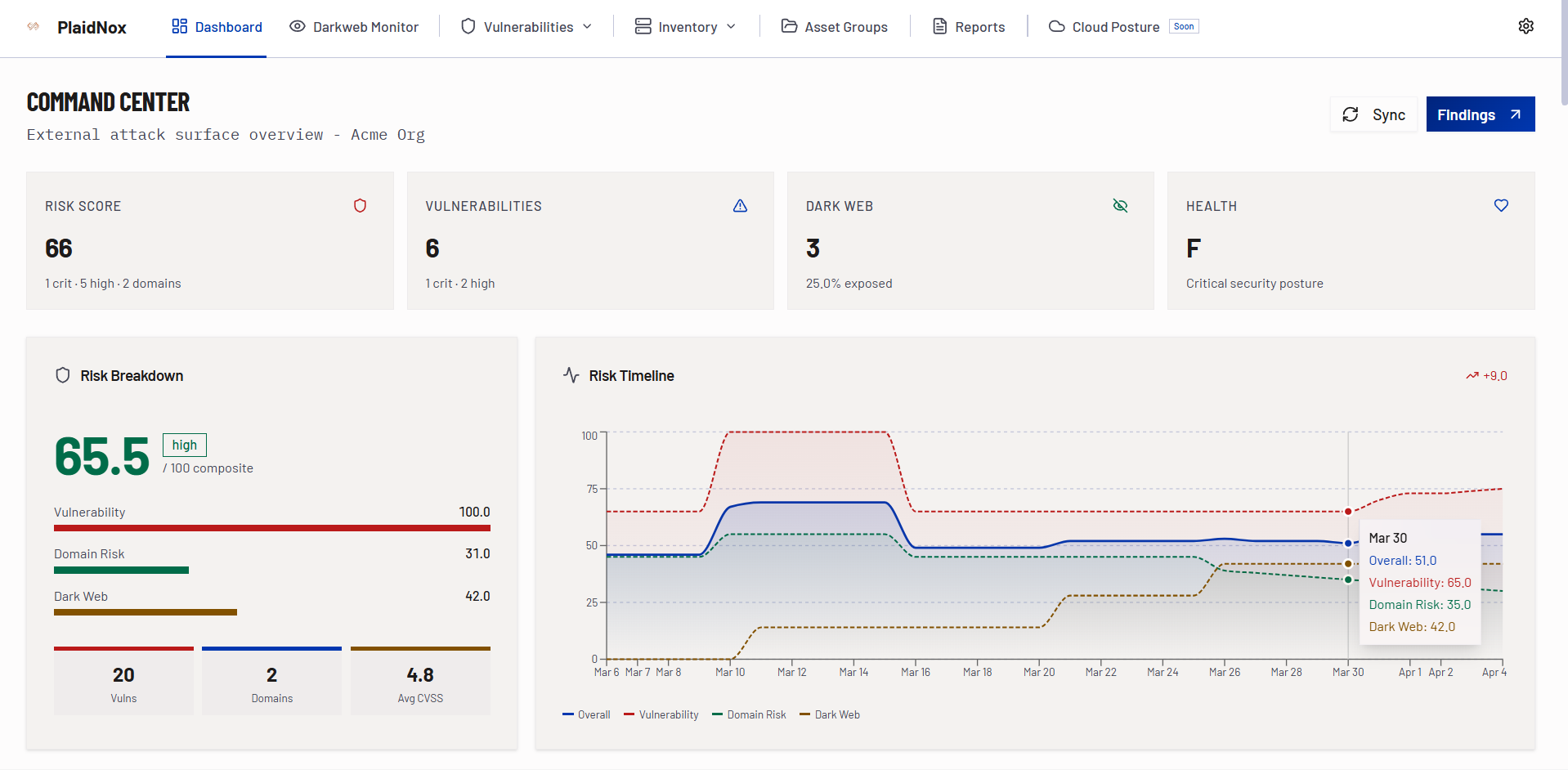
Veta Portal - Your Security Command Center
Manage all assets, track vulnerabilities in real time, monitor dark web exposures, and download reports - all from one unified portal with 16+ dashboard widgets.
- Real-time risk score & health grade
- Vulnerability severity breakdown
- OWASP Top 10 distribution
- Direct Jira & ServiceDesk integration
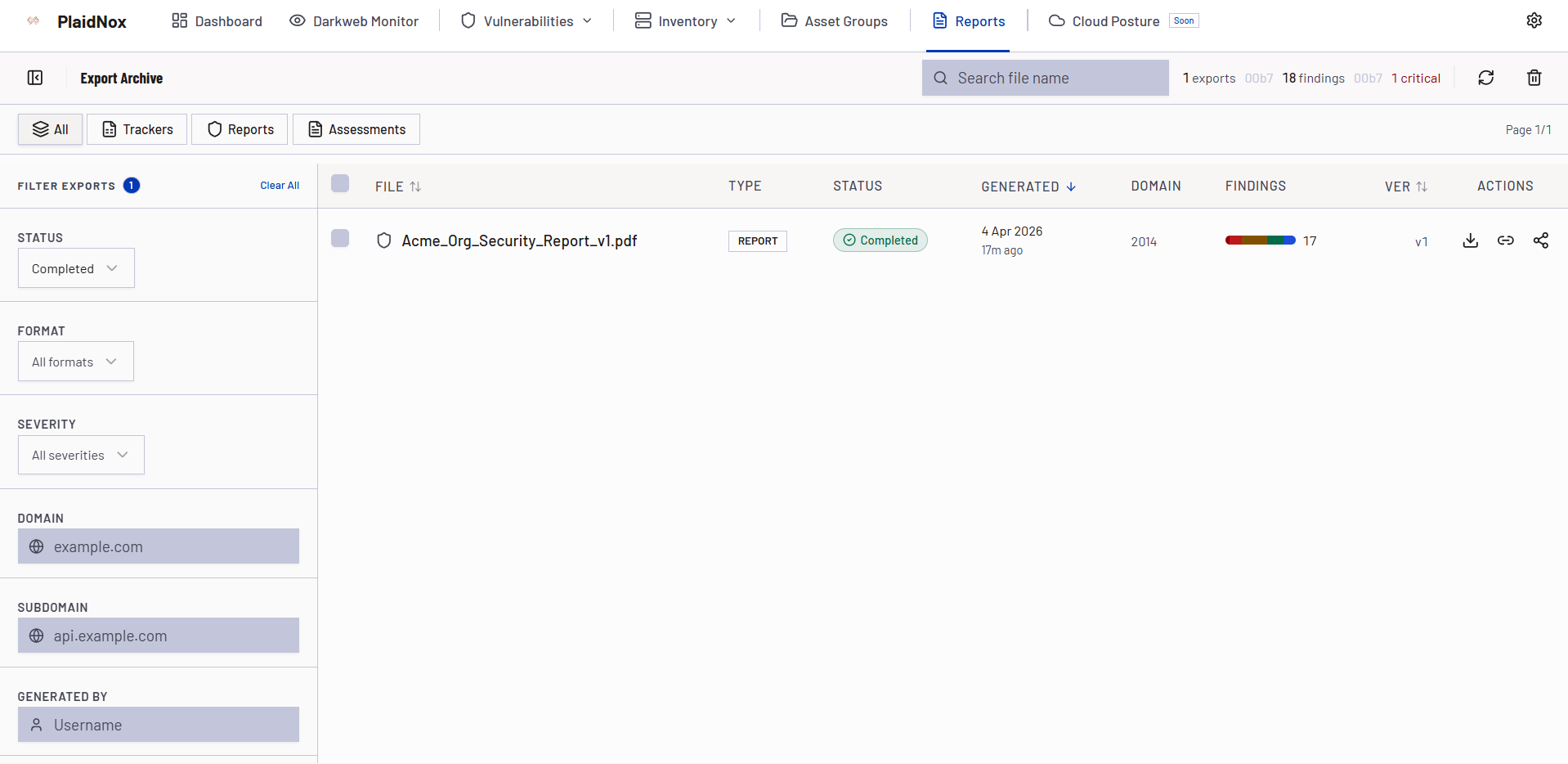
Reports That Drive Action
Every Veta scan generates PDF reports, XLSX vulnerability trackers, and network logs - so executives and engineers share the same view of risk and remediation progress.
- Executive summary with business-level risk posture
- Technical findings with CVSS scoring and AI enrichment
- Asset inventory with technology fingerprinting
- Remediation guidance mapped to engineering workflows
- Compliance mapping for OWASP, NIST, ISO 27001, PCI DSS, SOC 2
Why Security Teams Choose Veta
- 6 specialized scanners covering your entire attack surface
- 9 integrated platform modules in a single portal
- AI-enriched findings with automated remediation steps
- Dark web credential monitoring built in
- Multi-cloud CSPM for AWS, Azure, and GCP
- RBAC with 15 feature-level access controls
- Continuous monitoring with 7 notification channels
- Developer-friendly Jira & ServiceDesk integrations
Whether you're securing a growing startup or managing enterprise-scale infrastructure, Veta delivers the visibility and intelligence your team needs to stay ahead of threats.
Ready to Map Your Attack Surface?
Stop guessing what's exposed. Start with Veta and see every asset, vulnerability, and risk - in minutes.